Rc4 Stream Cipher And Its Variants Pdf File
Cipher and stream ciphers algorithms. In this paper, we compare the AES algorithm with different modes of operation (block cipher) and RC4 algorithm (stream cipher) in terms of CPU time, encryption time, memory utilization and throughput at different settings like variable key size and variable data packet size. An Introduction to New Stream Cipher Designs Tor E. Bj˝rstad University of Bergen, Norway Email: tor.bjorstad@ii.uib.no. RC4 should not be used for new applications even though it o ers. Risky and too di cult to get right. Unfortunately, the state of other popular stream ciphers is no less dire. The A5/1 cipher and its variants used.
This article is about the stream cipher. For other uses, see. RC4 General Designers First published Leaked in 1994 (designed in 1987) Cipher detail 40– 0000 bits State size 0000 bits ( 0000 effective) Rounds 1 Speed 7 cycles per byte on Modified Alleged RC4 on Intel Core 2: 13.9 cycles per byte In, RC4 (Rivest Cipher 4 also known as ARC4 or ARCFOUR meaning Alleged RC4, see below) is a.
While remarkable for its simplicity and speed in software, multiple vulnerabilities have been discovered in RC4, rendering it insecure. It is especially vulnerable when the beginning of the output is not discarded, or when nonrandom or related keys are used. Particularly problematic uses of RC4 have led to very insecure such as. As of 2015, there is speculation that some state cryptologic agencies may possess the capability to break RC4 when used in the. Has published to prohibit the use of RC4 in TLS; and have issued similar recommendations. A number of attempts have been made to strengthen RC4, notably Spritz, RC4A, and RC4 +. Contents.
History RC4 was designed by of in 1987. While it is officially termed 'Rivest Cipher 4', the RC acronym is alternatively understood to stand for 'Ron's Code' (see also, and ). RC4 was initially a, but in September 1994 a description of it was anonymously posted to the mailing list.
It was soon posted on the, where it was broken within days by Bob Jenkins. From there it spread to many sites on the Internet. The leaked code was confirmed to be genuine as its output was found to match that of proprietary software using licensed RC4. Because the algorithm is known, it is no longer a trade secret. The name RC4 is trademarked, so RC4 is often referred to as ARCFOUR or ARC4 (meaning alleged RC4) to avoid trademark problems. Has never officially released the algorithm; Rivest has, however, linked to the article on RC4 in his own course notes in 2008 and confirmed the history of RC4 and its code in a 2014 paper by him. RC4 became part of some commonly used encryption protocols and standards, such as in 1997 and in 2003/2004 for wireless cards; and in 1995 and its successor in 1999, until it was prohibited for all versions of TLS by in 2015, due to the weakening or breaking RC4 used in SSL/TLS.
The main factors in RC4's success over such a wide range of applications have been its speed and simplicity: efficient implementations in both software and hardware were very easy to develop. Description RC4 generates a (a ).
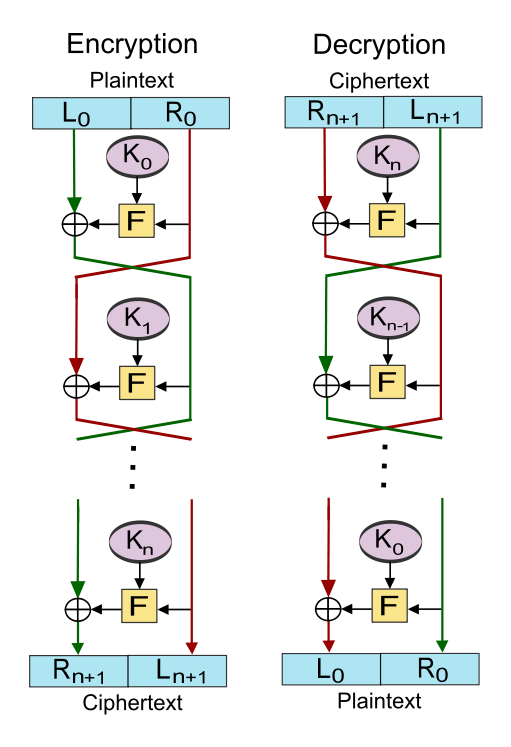
As with any stream cipher, these can be used for encryption by combining it with the plaintext using bit-wise; decryption is performed the same way (since exclusive-or with given data is an ). (This is similar to the except that generated pseudorandom bits, rather than a prepared stream, are used.) To generate the keystream, the cipher makes use of a secret internal state which consists of two parts:. A of all 256 possible (denoted 'S' below). Two 8-bit index-pointers (denoted 'i' and 'j'). The permutation is initialized with a variable length, typically between 40 and 2048 bits, using the algorithm (KSA). Once this has been completed, the stream of bits is generated using the pseudo-random generation algorithm (PRGA).
Key-scheduling algorithm (KSA) The algorithm is used to initialize the permutation in the array 'S'. 'keylength' is defined as the number of bytes in the key and can be in the range 1 ≤ keylength ≤ 256, typically between 5 and 16, corresponding to a of 40 – 128 bits. First, the array 'S' is initialized to the. S is then processed for 256 iterations in a similar way to the main PRGA, but also mixes in bytes of the key at the same time. For i from 0 to 255 Si:= i endfor j:= 0 for i from 0 to 255 j:= (j + Si + keyi keylength) mod 256 swap values of Si and Sj endfor Pseudo-random generation algorithm (PRGA). The lookup stage of RC4.
The output byte is selected by looking up the values of Si and Sj, adding them together modulo 256, and then using the sum as an index into S; S(Si + Sj) is used as a byte of the key stream, K. For as many iterations as are needed, the PRGA modifies the state and outputs a byte of the keystream.
In each iteration, the PRGA increments i, looks up the ith element of S, S i, and adds that to j, exchanges the values of S i and S j, and then uses the sum S i + S j (modulo 256) as an index to fetch a third element of S, (the keystream value K below) which is bitwise exclusive OR'ed ('ed) with the next byte of the message to produce the next byte of either ciphertext or plaintext. Each element of S is swapped with another element at least once every 256 iterations. I:= 0 j:= 0 while GeneratingOutput: i:= (i + 1) mod 256 j:= (j + Si) mod 256 of Si and Sj K:= S(Si + Sj) mod 256 output K endwhile RC4-based random number generators Several include arc4random, an API originating in providing access to a random number generator originally based on RC4.
In OpenBSD 5.5, released in May 2014, arc4random was modified to use. The implementations of arc4random in and 's libbsd also use ChaCha20. In the 2017 release of its and operating systems, Apple replaced RC4 with AES in its implementation of arc4random. for the new arc4random include the 'A Replacement Call for Random' for ARC4 as a mnemonic, as it provides better random data than does. Proposed new random number generators are often compared to the RC4 random number generator.
Several attacks on RC4 are able to. Implementation Many stream ciphers are based on (LFSRs), which, while efficient in hardware, are less so in software. The design of RC4 avoids the use of LFSRs and is ideal for software implementation, as it requires only byte manipulations. It uses 256 bytes of memory for the state array, S0 through S255, k bytes of memory for the key, key0 through keyk-1, and integer variables, i, j, and K. Performing a modular reduction of some value modulo 256 can be done with a with 255 (which is equivalent to taking the low-order byte of the value in question).
Bose Corporation
Test vectors These test vectors are not official, but convenient for anyone testing their own RC4 program. The keys and plaintext are, the keystream and ciphertext are in. Key Keystream Plaintext Ciphertext Key EB9F7781B734CA72A719. Plaintext BBF316E8D940AF0AD3 Wiki 6044DB6D41B7. Pedia 1021BF0420 Secret 04D46B053CA87B59. Attack at dawn 45A01F645FC44B9BF5 Security Unlike a modern stream cipher (such as those in ), RC4 does not take a separate alongside the key. This means that if a single long-term key is to be used to securely encrypt multiple streams, the protocol must specify how to combine the nonce and the long-term key to generate the stream key for RC4.
One approach to addressing this is to generate a 'fresh' RC4 key by a long-term key with a. However, many applications that use RC4 simply concatenate key and nonce; RC4's weak then gives rise to, like the (which is famous for breaking the standard). Because RC4 is a, it is more than common. If not used together with a strong (MAC), then encryption is vulnerable to a. The cipher is also vulnerable to a if not implemented correctly. It is noteworthy, however, that RC4, being a stream cipher, was for a period of time the only common cipher that was immune to the 2011 on. The attack exploits a known weakness in the way is used with all of the other ciphers supported by TLS 1.0, which are all block ciphers.
In March 2013, there were new attack scenarios proposed by Isobe, Ohigashi, Watanabe and Morii, as well as AlFardan, Bernstein, Paterson, Poettering and Schuldt that use new statistical biases in RC4 key table to recover plaintext with large number of TLS encryptions. The use of RC4 in TLS is prohibited by published in February 2015. Roos's biases and key reconstruction from permutation In 1995, Andrew Roos experimentally observed that the first byte of the keystream is correlated to the first three bytes of the key and the first few bytes of the permutation after the KSA are correlated to some linear combination of the key bytes. These biases remained unexplained until 2007, when Goutam Paul, Siddheshwar Rathi and Subhamoy Maitra proved the keystream-key correlation and in another work Goutam Paul and Subhamoy Maitra proved the permutation-key correlations. The latter work also used the permutation-key correlations to design the first algorithm for complete key reconstruction from the final permutation after the KSA, without any assumption on the key. This algorithm has a constant probability of success in a time which is the square root of the exhaustive key search complexity. Subsequently, many other works have been performed on key reconstruction from RC4 internal states.
Subhamoy Maitra and Goutam Paul also showed that the Roos type biases still persist even when one considers nested permutation indices, like SSi or SSSi. These types of biases are used in some of the later key reconstruction methods for increasing the success probability. Biased outputs of the RC4 The keystream generated by the RC4 is biased in varying degrees towards certain sequences making it vulnerable to. The best such attack is due to Itsik Mantin and who showed that the second output byte of the cipher was biased toward zero with probability 1/128 (instead of 1/256). This is due to the fact that if the third byte of the original state is zero, and the second byte is not equal to 2, then the second output byte is always zero. Such bias can be detected by observing only 256 bytes. And of showed that the first and the second bytes of the RC4 were also biased.
The number of required samples to detect this bias is 2 25 bytes. And David McGrew also showed such attacks which distinguished the keystream of the RC4 from a random stream given a gigabyte of output. The complete characterization of a single step of RC4 PRGA was performed by Riddhipratim Basu, Shirshendu Ganguly, Subhamoy Maitra, and Goutam Paul. Considering all the permutations, they prove that the distribution of the output is not uniform given i and j, and as a consequence, information about j is always leaked into the output. Fluhrer, Mantin and Shamir attack. Main article: In 2001, a new and surprising discovery was made by, and: over all possible RC4 keys, the statistics for the first few bytes of output keystream are strongly non-random, leaking information about the key.
If the nonce and long-term key are simply concatenated to generate the RC4 key, this long-term key can be discovered by analysing a large number of messages encrypted with this key. Burn in my light mp3 download. This and related effects were then used to break the ('wired equivalent privacy') encryption used with. This caused a scramble for a standards-based replacement for WEP in the 802.11 market, and led to the effort and. Protocols can defend against this attack by discarding the initial portion of the keystream. Such a modified algorithm is traditionally called 'RC4-dropn', where n is the number of initial keystream bytes that are dropped. The SCAN default is n = 768 bytes, but a conservative value would be n = 3072 bytes.
The Fluhrer, Mantin and Shamir attack does not apply to RC4-based SSL, since SSL generates the encryption keys it uses for RC4 by hashing, meaning that different SSL sessions have unrelated keys. Klein's attack In 2005, Andreas Klein presented an analysis of the RC4 stream cipher showing more correlations between the RC4 keystream and the key., and used this analysis to create aircrack-ptw, a tool which cracks 104-bit RC4 used in 128-bit WEP in under a minute. Whereas the Fluhrer, Mantin, and Shamir attack used around 10 million messages, aircrack-ptw can break 104-bit keys in 40,000 frames with 50% probability, or in 85,000 frames with 95% probability. Combinatorial problem A combinatorial problem related to the number of inputs and outputs of the RC4 cipher was first posed by and in 2001, whereby, of the total 256 elements in the typical state of RC4, if x number of elements ( x ≤ 256) are only known (all other elements can be assumed empty), then the maximum number of elements that can be produced deterministically is also x in the next 256 rounds.
This conjecture was put to rest in 2004 with a formal proof given by and. Royal Holloway attack In 2013, a group of security researchers at the Information Security Group at Royal Holloway, University of London reported an attack that can become effective using only 2 34 encrypted messages. While yet not a practical attack for most purposes, this result is sufficiently close to one that it has led to speculation that it is plausible that some state cryptologic agencies may already have better attacks that render RC4 insecure. Given that as of 2013 a large amount of traffic uses RC4 to avoid recent attacks on block ciphers that use, if these hypothetical better attacks exist, then this would make the TLS-with-RC4 combination insecure against such attackers in a large number of practical scenarios.
In March 2015 researcher to Royal Holloway announced improvements to their attack, providing a 2 26 attack against passwords encrypted with RC4, as used in TLS. Bar-mitzvah attack. Main article: On the Black Hat Asia 2015, Itsik Mantin presented another attack against SSL using RC4 cipher. NOMORE attack In 2015, security researchers from presented new attacks against RC4 in both and. Dubbed the Numerous Occurrence MOnitoring & Recovery Exploit (NOMORE) attack, it is the first attack of its kind that was demonstrated in practice. Their attack against can decrypt a secure within 75 hours. The attack against WPA-TKIP can be completed within an hour, and allows an attacker to decrypt and inject arbitrary packets.
RC4 variants As mentioned above, the most important weakness of RC4 comes from the insufficient key schedule; the first bytes of output reveal information about the key. This can be corrected by simply discarding some initial portion of the output stream. This is known as RC4-drop N, where N is typically a multiple of 256, such as 768 or 1024. A number of attempts have been made to strengthen RC4, notably Spritz, RC4A, and RC4 +. RC4A and have proposed an RC4 variant, which they call RC4A.
RC4A uses two state arrays S1 and S2, and two indexes j1 and j2. Each time i is incremented, two bytes are generated:. First, the basic RC4 algorithm is performed using S1 and j1, but in the last step, S1 i + S1 j1 is looked up in S2. Second, the operation is repeated (without incrementing i again) on S2 and j2, and S1S2 i+S2 j2 is output. Thus, the algorithm is: All arithmetic is performed modulo 256 i:= 0 j1:= 0 j2:= 0 while GeneratingOutput: i:= i + 1 j1:= j1 + S1i of S1i and S1j1 output S2S1i + S1j1 j2:= j2 + S2i swap values of S2i and S2j2 output S1S2i + S2j2 endwhile Although the algorithm required the same number of operations per output byte, there is greater parallelism than RC4, providing a possible speed improvement. Although stronger than RC4, this algorithm has also been attacked, with Alexander Maximov and a team from NEC developing ways to distinguish its output from a truly random sequence.
Main article: Variably Modified Permutation Composition (VMPC) is another RC4 variant. It uses similar key schedule as RC4, with j:= S(j + Si + keyi mod keylength) mod 256 iterating 3 x 256 = 768 times rather than 256, and with an optional additional 768 iterations to incorporate an initial vector. The output generation function operates as follows: All arithmetic is performed modulo 256. I:= 0 while GeneratingOutput: a:= Si j:= Sj + a output SSSj + 1 Swap Si and Sj ( b:= Sj; Si:= b; Sj:= a)) i:= i + 1 endwhile This was attacked in the same papers as RC4A, and can be distinguished within 2 38 output bytes. RC4 + RC4 + is a modified version of RC4 with a more complex three-phase key schedule (taking about 3× as long as RC4, or the same as RC4-drop512), and a more complex output function which performs four additional lookups in the S array for each byte output, taking approximately 1.7× as long as basic RC4.
All arithmetic modulo 256. are left and right shift, ⊕ is exclusive OR while GeneratingOutput: i:= i + 1 a:= Si j:= j + a Swap Si and Sj ( b:= Sj; Si:= b; Sj:= a) c:= Si3 + Sj3 output (Sa+b + Sc⊕0xAA) ⊕ Sj+b endwhile This algorithm has not been analyzed significantly.
Spritz In 2014, Ronald Rivest gave a talk and co-wrote a paper on an updated redesign called. A hardware accelerator of Spritz was published in Secrypt, 2016.
The authors have shown that due to multiple nested calls required to produce output bytes, Spritz performs rather slowly compared to other hash functions such as SHA-3 and best known hardware implementation of RC4. The algorithm is: All arithmetic is performed modulo 256 while GeneratingOutput: i:= i + w j:= k + Sj + Si k:= k + i + Sj swap values of Si and Sj output z:= Sj + Si + Sz + k endwhile The value w, is to the size of the S array. So after 256 iterations of this inner loop, the value i (incremented by w every iteration) has taken on all possible values 0.255, and every byte in the S array has been swapped at least once. Like other, Spritz can be used to build a cryptographic hash function, a deterministic random bit generator , an encryption algorithm that supports with associated data (AEAD), etc. Spritz was broken by Banik and Isobe. Prasithsangaree & P.
Krishnamurthy (2003). Archived from (PDF) on 3 December 2013. Retrieved 22 September 2015. ^ Andrei Popov (February 2015). Lucian Constantin (14 May 2014). Lindell (2014), Introduction to Modern Cryptography, Chapman and Hall/CRC, p. 77.
^ John Leyden (6 September 2013). The Register. Retrieved 2015-01-03. 12 November 2013.
Retrieved 2013-12-04. (Mailing list). 9 September 1994. Archived from on 22 July 2001. Retrieved 2007-05-28. Bob Jenkins (1994-09-15).:.
Retrieved 23 June 2014. ^ Rivest, Ron; Schuldt, Jacob (27 October 2014). Retrieved 26 October 2014. Retrieved 21 September 2014. (21 July 2014). BSD Cross Reference, OpenBSD src/lib/. Retrieved 2015-01-13.
ChaCha based random number generator for OpenBSD. riastradh, ed. (16 November 2014). BSD Cross Reference, NetBSD src/lib/. Retrieved 2015-01-13. Legacy arc4random(3) API from OpenBSD reimplemented using the ChaCha20 PRF, with per-thread state.
Retrieved 6 January 2015. Retrieved 6 January 2016.
Bartosz Zoltak. Chefranov, A.G.
^ Itsik Mantin, (2001). (PDF): 152 – 164. CS1 maint: Uses authors parameter. RSA Laboratories. 1 September 2001. Sklyarov, Dmitry (2004).
A-List Publishing. Isobe, Takanori; Ohigashi, Toshihiro (10–13 Mar 2013).
Hiroshima University. Retrieved 2014-10-27. Pouyan Sepehrdad; Serge Vaudenay; Martin Vuagnoux (2011). Lecture Notes in Computer Science. 6544: 74–91. Green, Matthew. Cryptography Engineering.
Retrieved 12 March 2013. Nadhem AlFardan; Dan Bernstein; Kenny Paterson; Bertram Poettering; Jacob Schuldt.
Royal Holloway University of London. Retrieved 13 March 2013.
Andrew Roos. A Class of Weak Keys in the RC4 Stream Cipher.
Two posts in sci.crypt, message-id 43u1eh$1j3@hermes.is.co.za and 44ebge$llf@hermes.is.co.za, 1995. Goutam Paul, Siddheshwar Rathi and Subhamoy Maitra. On Non-negligible Bias of the First Output Byte of RC4 towards the First Three Bytes of the Secret Key.
Proceedings of the International Workshop on Coding and Cryptography (WCC) 2007, pages 285–294 and Designs, Codes and Cryptography Journal, pages 123–134, vol. 1-3, December 2008. Goutam Paul and Subhamoy Maitra. Permutation after RC4 Key Scheduling Reveals the Secret Key. SAC 2007, pages 360–377, vol. 4876, Springer.
Eli Biham and Yaniv Carmeli. Efficient Reconstruction of RC4 Keys from Internal States. FSE 2008, pages 270–288, vol.
5086, Lecture Notes in Computer Science, Springer. Mete Akgun, Pinar Kavak, Huseyin Demirci.
New Results on the Key Scheduling Algorithm of RC4. INDOCRYPT 2008, pages 40–52, vol. 5365, Lecture Notes in Computer Science, Springer.
Riddhipratim Basu, Subhamoy Maitra, Goutam Paul and Tanmoy Talukdar. On Some Sequences of the Secret Pseudo-random Index j in RC4 Key Scheduling. Proceedings of the 18th International Symposium on Applied Algebra, Algebraic Algorithms and Error Correcting Codes (AAECC), 8–12 June 2009, Tarragona, Spain, pages 137–148, vol. 5527, Lecture Notes in Computer Science, Springer.
Subhamoy Maitra and Goutam Paul. New Form of Permutation Bias and Secret Key Leakage in Keystream Bytes of RC4. Proceedings of the 15th Fast Software Encryption (FSE) Workshop, 10–13 February 2008, Lausanne, Switzerland, pages 253–269, vol. 5086, Lecture Notes in Computer Science, Springer. (PDF): 52 – 67.
CS1 maint: Uses authors parameter. Scott R. Fluhrer, David A. (PDF): 19 – 30.
CS1 maint: Uses authors parameter. Basu, Riddhipratim; Ganguly, Shirshendu; Maitra, Subhamoy; Paul, Goutam (2008). 'A Complete Characterization of the Evolution of RC4 Pseudo Random Generation Algorithm'.
Journal of Mathematical Cryptology. 2 (3): 257–289.
Fluhrer, Itsik Mantin and Adi Shamir, Weaknesses in the Key Scheduling Algorithm of RC4. 2001, pp1 – 24. in the 'Standard Cryptographic Algorithm Naming' database. Ron Rivest.
Klein, Attacks on the RC4 stream cipher, Designs, Codes and Cryptography (2008) 48:269–286. Erik Tews, Ralf-Philipp Weinmann, Andrei Pyshkin. and, A New Weakness in the RC4 Keystream Generator and an Approach to Improve the Security of the Cipher. – FSE 2004, pp245 – 259.
John Leyden (15 March 2013). The Register. AlFardan; et al. (8 July 2013). Information Security Group, Royal Holloway, University of London. Information Security Group, Royal Holloway, University of London. Retrieved 2013-09-06.
(website). Retrieved November 19, 2016. Retrieved November 19, 2016.
Subhamoy Maitra
Mathy Vanhoef and Frank Piessens (9 August 2015).